DozWPSecure User Manual
Requirements
- WordPress 4.x, 5.0 or higher.
Installation Guide
Automated Installation (via WordPress Admin Dashboard)
- Go to Plugins > Add New.
- Search for “DozWPSecure” after clicking on “Add New” button.
- Install the plugin.
- Activate it right away.
Manual Installation (via WordPress Admin Dashboard)
After downloading the DozWPSecure zip file,
- Log in to the WordPress administrator panel (wp-admin).
- Go to Plugins >Add New>Upload Plugin.
- Click “Choose File” and select the downloaded zip file.
- Click “Install Now” button.
- Click “Activate Plugin” button for activating the DozWPSecure plugin.
Manual Installation (via File Manager)
After downloading and extracting the DozWPSecure zip file,
- Upload the entire DozWPSecure folder to the /wp-content/plugins/ directory via web hosting File Manager / FTP / SCP.
- Log in to the WordPress administrator panel (wp-admin).
- Go to Plugins > Installed Plugins.
- Click on “Activate” link for activating the DozWPSecure plugin.
If the installation does not succeed, please contact us for help. After the installation is finished, DozWPSecure will appear in the Menu list.
Privacy Notices
With the default configuration, this plugin does not:
- track users by stealth
- write any user personal data to the database
- send any data to external servers
- show any ads
Securing your WordPress website
Navigate to “DozWPSecure” menu to start working on the hardening settings.
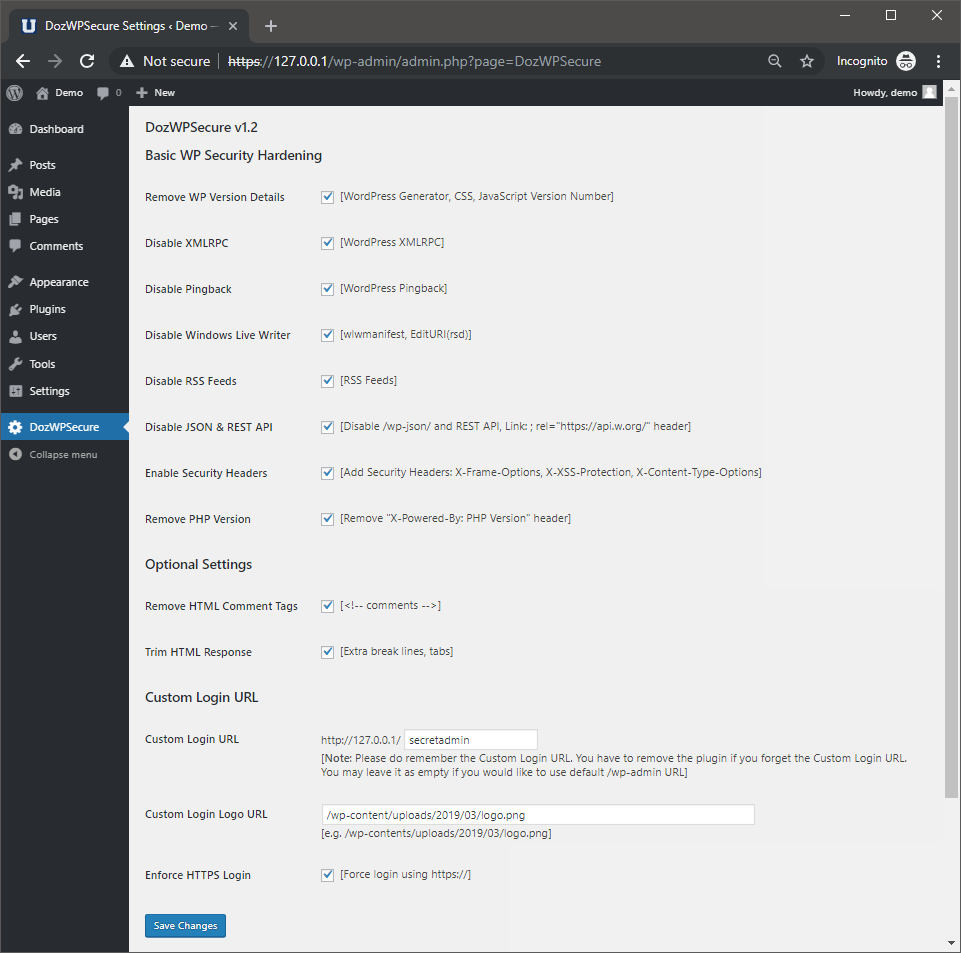
Basic WP Security Hardening
- Remove WP Version Details
Exposing the WordPress version number is not a good practice because the attacker can easily identify if you are still using any known vulnerable version. By removing/hiding the version number, you will make the version number enumeration to be harder. This function will remove the WordPress core version number that is exposed in the HTML page source.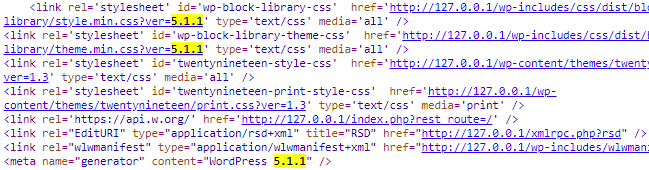
- Disable XMLRPC
This to prevent remote updates to WordPress from other applications. By disabling this feature, you eliminate the risk of external attacks gaining access remotely through the XML-RPC feature.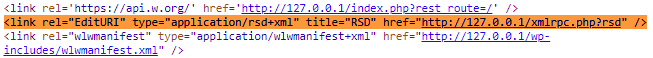
- Disable Pingback
A pingback is a special type of comment that’s created when you link to another blog post, as long as the other blog is set to accept pingbacks. By disabling this feature, you will reduce the spam coming from people who just want to get a link of any sort posted on your content.
- Disable Windows Live Writer
Windows Live Writer (WLW) is a blog publishing application developed by Microsoft. By disabling this feature, you eliminate the risk of external attacks gaining access remotely through Windows Live Writer.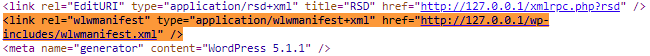
- Disable RSS Feeds
RSS feeds allow users to subscribe to your blog posts. However, when building small static or company websites, you may want to turn off the RSS feeds.![]()
- Disable JSON & REST API
JSON REST API will allow users to retrieve data in JSON format using GET requests, which is useful for those building apps with WordPress. However, most site owners may not be needing those features at all. This will effectively prevent unauthorized requests from using the REST API to get information from your website.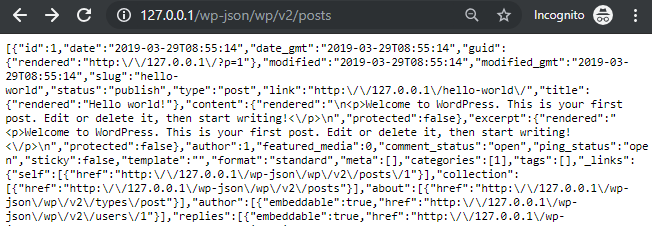
- Enable Security Headers (X-Frame-Options, X-XSS-Protection, X-Content-Type-Options)
HTTP security headers provide yet another layer of security by helping to mitigate attacks and security vulnerabilities.
- Remove PHP Version Header
PHP version header information can help an attacker gain a greater understanding of the systems in use and potentially develop further attacks targeted at the specific version of PHP. An attacker might use the disclosed information to harvest specific security vulnerabilities for the identified version.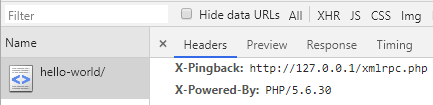
Optional Settings
- Remove HTML Comment Tags
This will help to remove HTML comment tags to prevent information leakage (e.g. developer comments, hardcoded credentials, bug fixes, etc).
- Trim HTML Response
Trimming HTML response will help to reduce the size of the web page.
Custom Login URL
- Customize Login URL
This allows you to change the default WordPress admin login URL to another name. The user will be redirected to the homepage if the URL is invalid. It will help to prevent the attacker to easily guess and brute force attack on your login page.
- Customize Login Logo URL
This will allow you to change the default WordPress logo on your admin login page.
- Enforce HTTPS Login
This will redirect the user to HTTPS when accessing the WordPress admin login URL.